OpenVPN is an open-source commercial software that implements Virtual Private Network (VPN) techniques to create secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It uses a custom security protocol that utilizes SSL/TLS for key exchange. It is capable of traversing Network Address Translators (NATs) and Firewalls. It was written by James Yonan and is published under the GNU General Public License.
Use Case
Some times you need to connect to your Virtual Datacenter over a Secured network. The commercial applications like, Palo Alto are very expensive. OpenVPN is an opensource implementation of IP/VPN server. You can install OpenVPN in your VDC and bring all your virtual machines under this Server. Later you will be connected to your VDC using this server.
Deployment
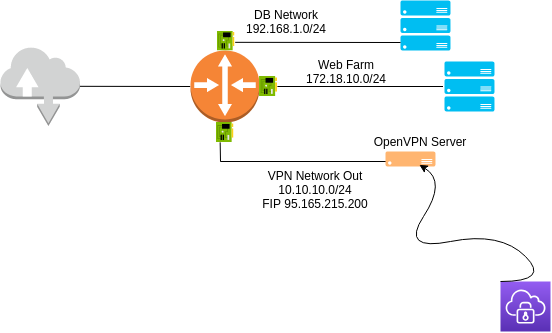
A high level diagram of the Deployment
Setup
We have Three networks:
- DB Network - 192.168.1.0/24
- Web Farm - 172.18.10.0/24
- VPN Network Out - 10.10.10.0/24
Virtual Machines under First two networks doesn’t have a Floating IP Address. The third network, VPN Network Out, in this network we created Our VPN Server. And we will assign a Floating IP Address to this Server.
Installation
- Create a Virtual Server. Preferably Ubuntu 16.04
- Download or clone the Installation Script from our GitHub Here
Make the script executable by this command:
sudo chmod +x openvpn-install.sh
Now run the script with the following command:
sudo bash openvpn-install.sh
The following screen will be Displayed.
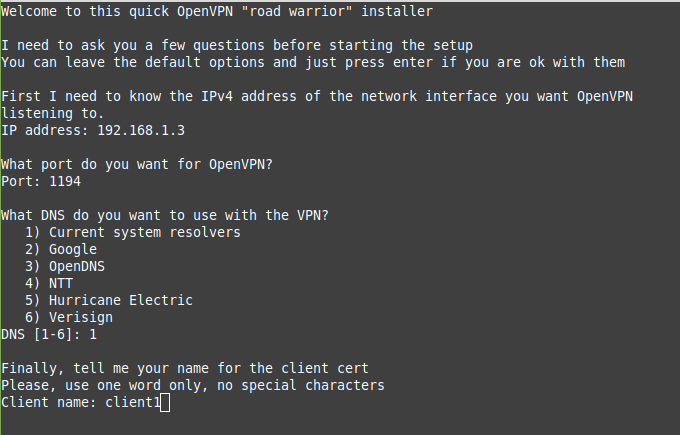
- Script will Automatically Detect the Internal IP Address.
- By default
1194UDP port will be used. You can change this if you need. - The preferred DNS, in this tutorial we choose Google DNS.
- Finally, Enter a name for your Client Configuration file.
- Hit Enter, and sit back.
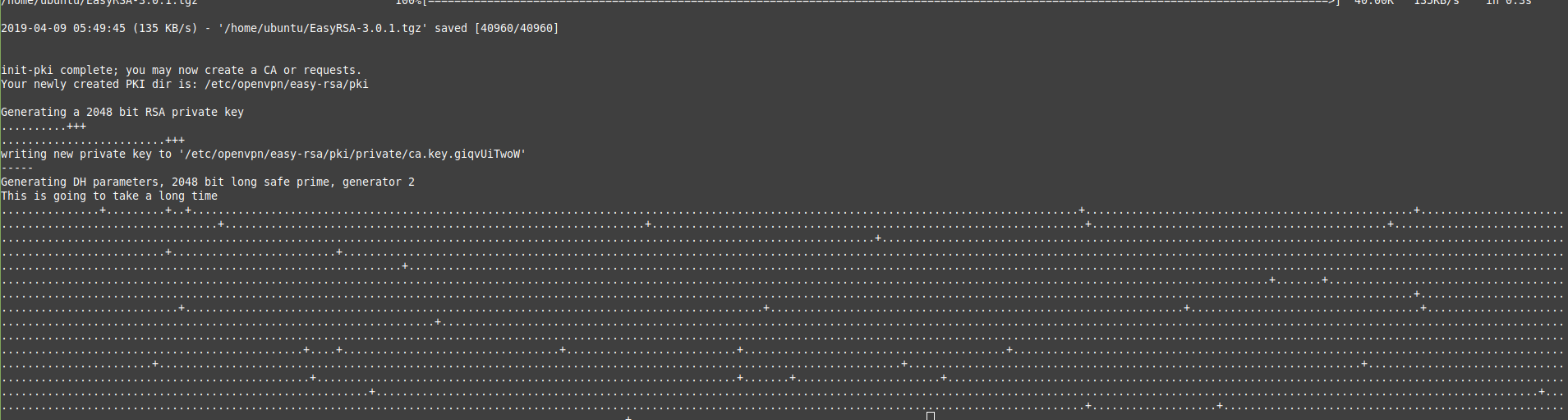
Script will automatically Download a lot of files and creating Certificates.
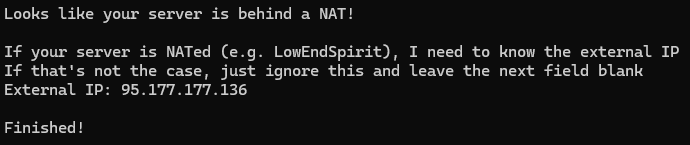
Finally it will ask for your Floating IP Address, enter it and Finished.
Client Configuration
- Download the Appropriate client from here
- Install it
- Open the Application
- Import the File, Choose your Client Configuration
- It will show a Window, saying that You are Connected
Make sure you have added a Security Group rule for port 1194 UDP for the VPN Server.
And three Interfaces added for your Router. This is for three Networks.